Sitecore ships with a number of out-of-the-box roles that provide feature access. For this article, we're going to ignore the out-of-the-box roles as well as permissions to specific Sitecore features. Instead, we will concentrate on areas where you would typically need to create your own custom roles and implement custom security, or more specifically, the permissions a Content Author requires to edit content.
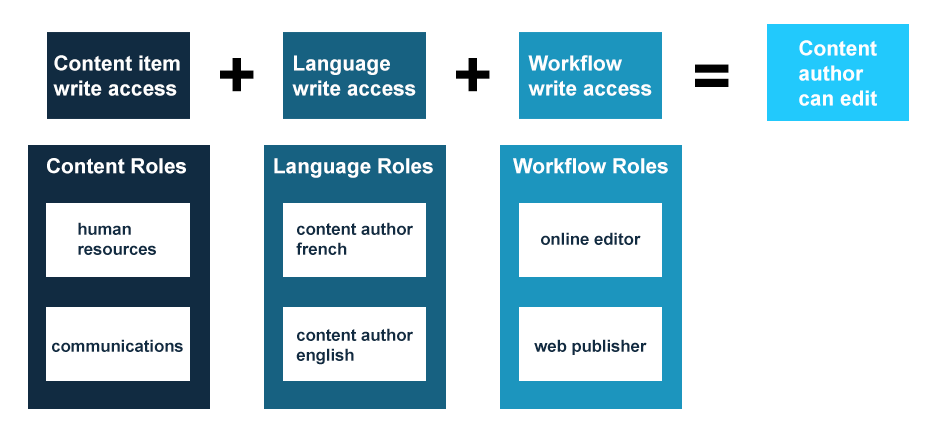
In Sitecore, a Content Author's ability to edit content is dictated by 3 key areas:
- Write access to the content item you are attempting to edit. These items are the pages in your site, the datasources of your components, the media in the media library, etc.
- Language Write access to the language in which you are making the edit
- Workflow Write access to the workflow state of the current item

If the Content Author lacks any of these permissions, they cannot edit an item.
As a best practice, we secure each of these areas of the tree separately to custom roles we create. We create a Content Item role, a Language Access role (if there are multiple languages in play) and a Workflow Access role. By keeping the roles separate rather than securing all permissions to a single role, we can create an incredibly granular security implementation, especially as the complexity of your build increases. For example, as you roll out additional sites or start securing your single site into areas of ownership, you can create additional Content Item roles, as you start supporting multiple languages in your site, you can create additional Language roles, and as the number of states in your workflow expands, you can create additional Workflow roles.
So what does this look like in practice? Well, here is an illustration of what an actual implementation might look like with sample roles corresponding to each of the three pillars, using the above diagram as a base:
In such a scenario, let's assume you have an area of your content tree secured so that only individuals belonging to the Human Resources department can edit the content. You may have a need to vary the assignment of editing permissions to fulfill the following scenario:
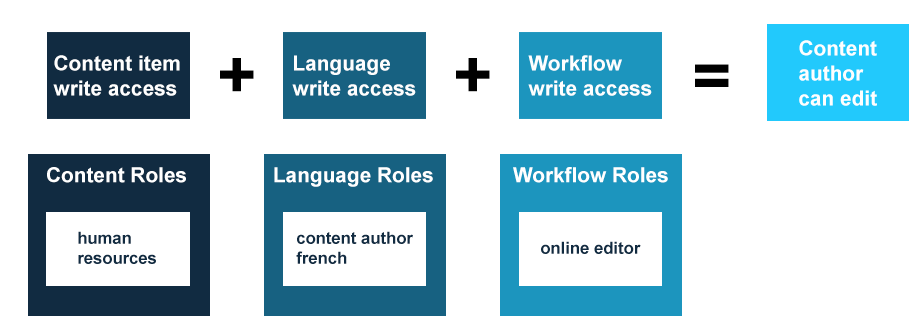
- Scenario #1: A Human Resources, French only, Online Editor
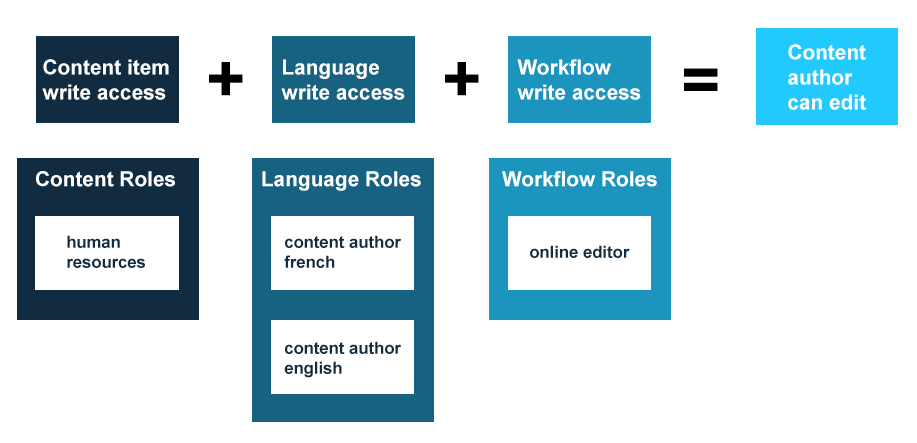
- Scenario #2: A Human Resources, both French and English, Web Publisher
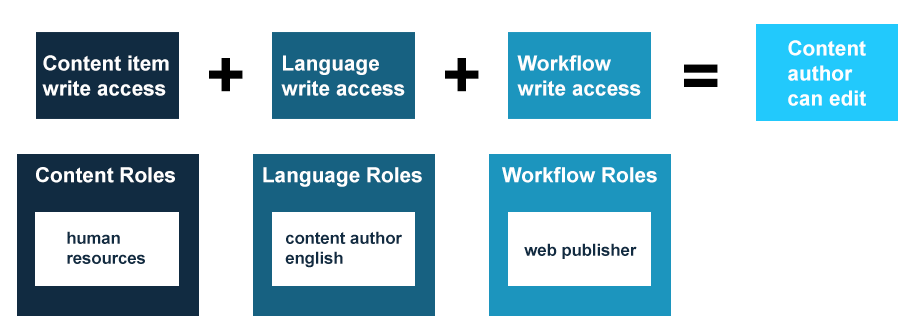
- Scenario #3: A Human Resources, English only, Web Publisher
Here's how these scenarios (and more) can be achieved with the roles outlined above, while maintaining all the prerequisites necessary to edit content:
Scenario #1
Scenario #2
Scenario #3
As scenario #2 illustrates, you can even add more than one role from a single pillar to expand permissions in that area. In this case, we gave the content author permissions to both languages by making them a member of both the Content Author English and Content Author French roles.
I should add, although this approach provides for a granular security implementation, if you have a specific security scenario that is repeated across a number of users, you can make your life easier by creating a super role. For example, for scenario #1 you could create a custom role that is a member of all three of the Human Resources, Content Author French, and Online Editor roles. Instead of assigning all three roles to a single user, you can simply assign the user to the super role and all permissions from the other roles will be applied. This approach keeps your security granular yet allows for quick assignment of common responsibilities.
As you can see, this particular model can be very flexible and can help future proof your security implementation by isolating security to these pillar-specific roles.
Continue to Sitecore Security Part 2: The Security Editor and Access Viewer.






